Cybersecurity is a vital activity for utilities. And it’s a lot simpler to implement than you may think.
Today most distribution system operators (DSO) are using modern interconnected systems and digital communication when operating their power system assets. Although most of the operational networks of DSOs are not directly connected to the Internet, in today’s digital age, there are no truly separate and secure systems anymore. This means that establishing cybersecurity is a vital activity for all DSOs and, in the end, for their customers to ensure the continued availability of power supply.
Do we need to consider protection relays as elements of cybersecurity?
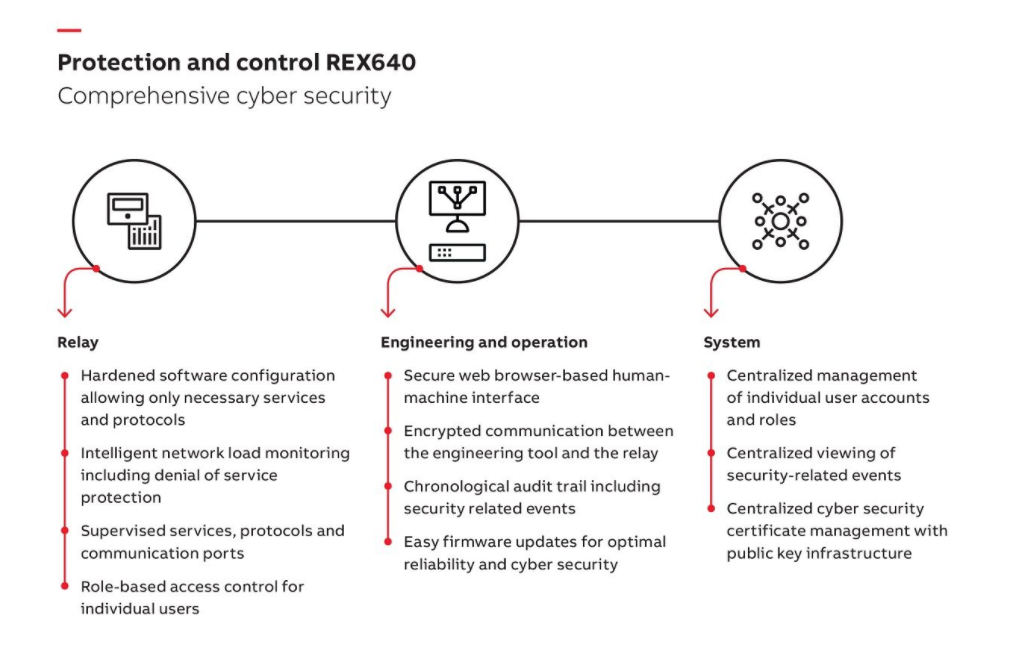
As protection relays are a part of power systems, they must also be a part of cybersecurity solutions. Naturally, connections interfacing the Internet and upper level control software are of vital importance to cybersecurity. However, cybersecurity in all components on the system level closer to the primary process must also be strengthened. This is known as defense-in-depth principle.
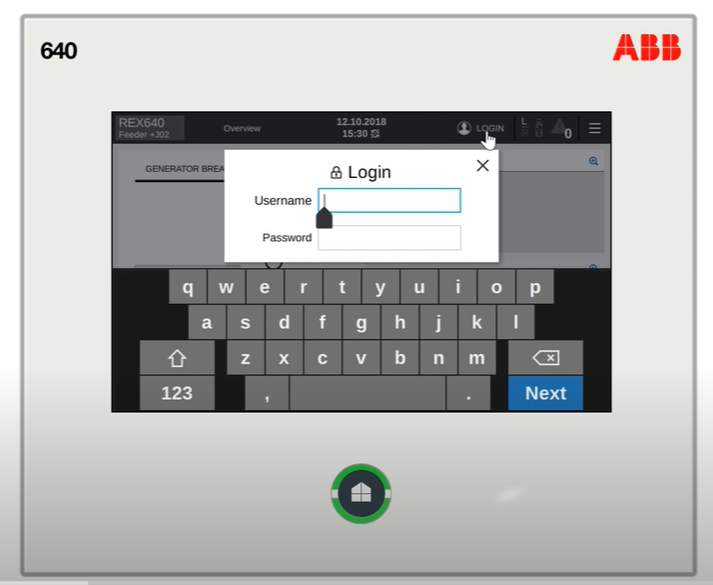
The target is to improve confidentiality (i.e. information is accessed only by an authorized person or entity), integrity (i.e. data or information can be trusted) and availability of the system (i.e. it’s available when required). In protection relays this means enabling for example user authentication, security logging and secure communication functionalities.
For interoperability and usability, it is important that these improvements are done according to definition of the relevant industry standards, e.g. IEC 62443 and IEC 62351.
How to ensure system resilience with protection relay?
Besides cybersecurity, DSOs need to take care of cyber resilience. Cyber resilience includes not only the technical security features in the products and their usage but also topics such as how the system works or recovers in case of a possible cyber-attack. For abnormal situations we can utilize denial-of-service protection and alarming in the protection relays. For system recovery it is important that there are plans and processes available, e.g. there are regular back-ups of protection relay configurations. All this behavior increases the topmost requirement for protection relay: availability of the power system.
Everything is based on proper training of users and enforcement of the cybersecurity policies. Without these the foundation for a secure system does not exists.
Forget complexity – you know the methods already
You may think that cybersecurity requirements make products and systems very complicated, but that’s not the case.
To increase security and resilience to the power system, it is important to configure the system in an efficient way. There are several methods to improve the usability of the cybersecurity aspects.
You already know these methods, as they are used in every day information technology (IT) activities in offices: centralized user authentication using Active Directory servers, centralized security logging using Syslog and standard encryption algorithms in communication using Public Key Infrastructure (PKI).
At ABB we are already writing the future of energy. Comprehensive cybersecurity has been one of the crucial points in developing of our new all-in-one protection and control relay REX640. User authentication, security logging and secure configuration tool link are essential parts of REX640.
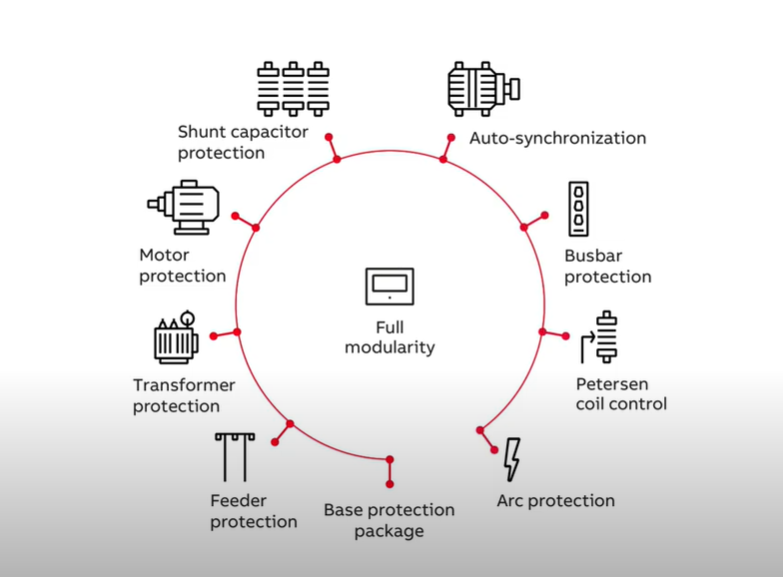
 REX640 makes protecting all your assets in advanced power generation and distribution applications easy. The fully modular design allows unequaled customization and modification flexibility, and easy adaptation to changing protection requirements throughout the relay life cycle. This is asset management at its best. As the newest member of ABB’s Relion® protection and control family of relays, REX640 further reinforces Relion’s position as the range of relays to rely on.
REX640 makes protecting all your assets in advanced power generation and distribution applications easy. The fully modular design allows unequaled customization and modification flexibility, and easy adaptation to changing protection requirements throughout the relay life cycle. This is asset management at its best. As the newest member of ABB’s Relion® protection and control family of relays, REX640 further reinforces Relion’s position as the range of relays to rely on.